How the Pandemic Lit a Fire Under Cyber Stocks
The U.S. Department of Justice declared 2020 as the “worst year ever” for extortion-related cyberattacks.
And the first half of 2021 has already seen a 102% spike compared to the same period last year. It was a crisis already burning, but the pandemic added gasoline to the fire.
When the government expanded unemployment benefits to folks thrown out of work by the pandemic, cybercriminals stepped in, filing unemployment claims using victims’ personal data.
• Identity theft was even used by cyber thugs to steal federal stimulus checks.
In total, 394,280 reports of government benefits fraud were submitted last year … a steep rise from the 12,900 reports in 2019.
Also, as millions of people shifted to remote work — including workers with access to critical infrastructure — hackers employed another favorite strategy:
• Ransomware is a palette of tools allowing hackers to access computer systems to disrupt or lock them down … until they get paid.
According to Eric Cole, President Obama’s cybersecurity commissioner and author of the book “Cyber Crisis”:
Critical infrastructure was always designed to have the control systems isolated and physically separate from the corporate network and the internet. Initially for automation and accelerated by the pandemic, these systems are now connected to the internet … the known vulnerabilities make them an easy target.
The list of potential targets is a mile long, including energy, financial services, water, transportation, health care, food and agriculture. Hobbling any of these would have a devastating effect on the U.S. economy … not to mention our personal health and security.
Recent Attacks Out of Russia
The June attack on meat producer JBS, for example — which supplies more than 20% of all beef in America — was attributed to a Russian cybercriminal group named REvil, which earlier tried to extort Apple (Nasdaq: AAPL) supplier Quanta Computer.
REvil is similar to DarkSide, which is said to be behind the ransomware attack that shut down the Colonial Pipeline in May. REvil and DarkSide essentially operate as “ransomware-as-a-service,” employing large staffs that carry out attacks or help others execute ransomware attacks … while they take a nice cut of the profits.
Paying ransom is frowned upon as it only encourages more attacks. But companies often have little choice in order to get back up and running. JBS hasn’t disclosed whether it paid a ransom; Colonial Pipeline’s CEO admitted to paying $4.4 million to resume operations.
The nightmare scenario would be a massive cyber-shutdown of hospitals and healthcare systems. An analysis conducted between March and November 2020 by the U.S. Cybersecurity and Infrastructure Security Agency (CISA) showed that 49% of healthcare providers surveyed had “risky ports and services” … and 58% of them were using software vulnerable to attack.
And it’s already happening. Up to 560 healthcare facilities were hit by ransomware last year. Last October, ransomware claimed its first life: A ransomware attack caused the failure of IT systems at a major hospital in Duesseldorf, Germany, resulting in the death of a patient.
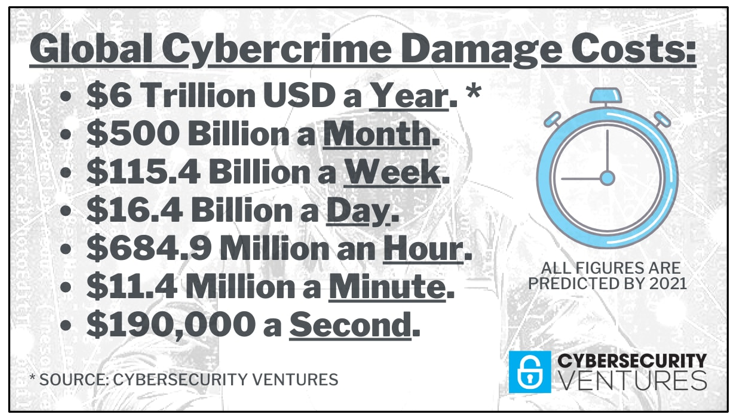
Cybercrime Costs Soar
Think about all the lost productivity arising from disruption to the normal course of business, forensic investigations, restoration of hacked data and systems … not to mention reputational harm.
Each and every minute, $2,900,000 is lost to cybercrime.
It’s no exaggeration to call cybercrime the greatest transfer of wealth in history. It accounts for more monetary damage than all natural disasters in a given year, and it’s predicted to be more profitable than the global trade of all major illegal drugs combined!
Unsurprisingly, all this has lit a fire under cybersecurity stocks.
• In 2004, the global cybersecurity market was worth $3.5 billion. By 2017, it was worth more than $120 billion … roughly 35 times larger.
The healthcare industry alone is predicted to spend $125 billion from 2020 through 2025.
How Can YOU Play This Monstrous Megatrend?
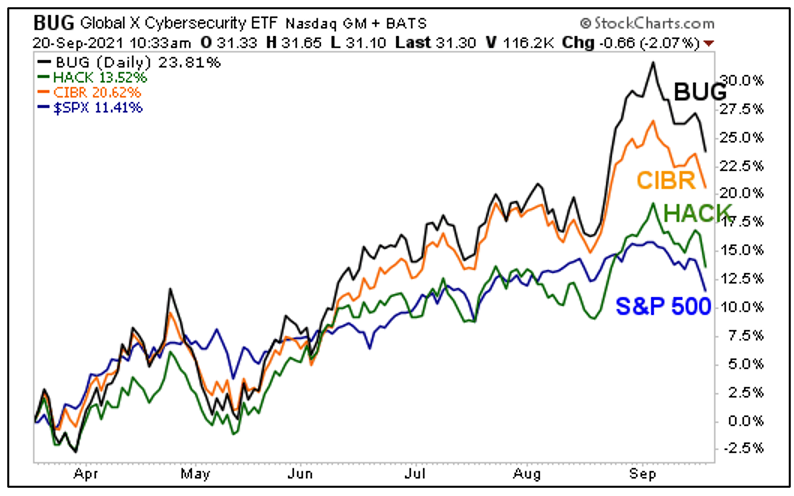
You could buy individual stocks, but if your appetite for risk is lower, I’d strongly suggest looking into the following exchange-traded funds (ETFs).
ETF 1: ETFMG Prime Cyber Security ETF (NYSE: HACK) tracks the Prime Cyber Defense Index and holds 60 securities in its basket, including companies offering hardware, software, consulting and services to defend against cybercrime. Expense ratio: 0.60%
ETF 2: First Trust NASDAQ Cybersecurity ETF (Nasdaq: CIBR) follows the Nasdaq CTA Cybersecurity Index, which measures the performance of companies engaged in the cybersecurity segment of the technology and industrials sectors. It holds 39 stocks in its basket. Expense ratio: 0.60%
ETF 3: Global X Cybersecurity ETF (Nasdaq: BUG) follows the Indxx Cybersecurity Index. It offers exposure to 32 stocks … companies that stand to benefit from the increased adoption of cybersecurity technology. Expense ratio: 0.50%
Here’s a performance chart of these three funds and the S&P 500 over the last six months.
You can see that when the market was hot, these funds led the way higher. Now with the market cooling off, they are giving back a bit. If you want to get long any of these cybersecurity funds, your buying opportunity may be coming up.
Remember to do your own due diligence before buying anything.
All the best,
Sean